×
![]()
Versions used
- Netbeans IDE 8.2
- Mocha 4.0.1 – Our Testing Tool
- Chai 4.1.2 – An Assert Library
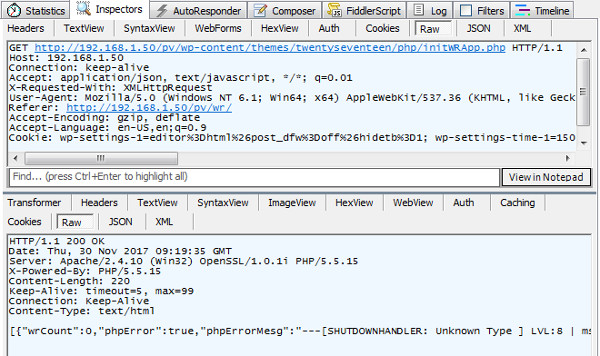
Create a HTML5 Project with Javascript Support inside Netbeans
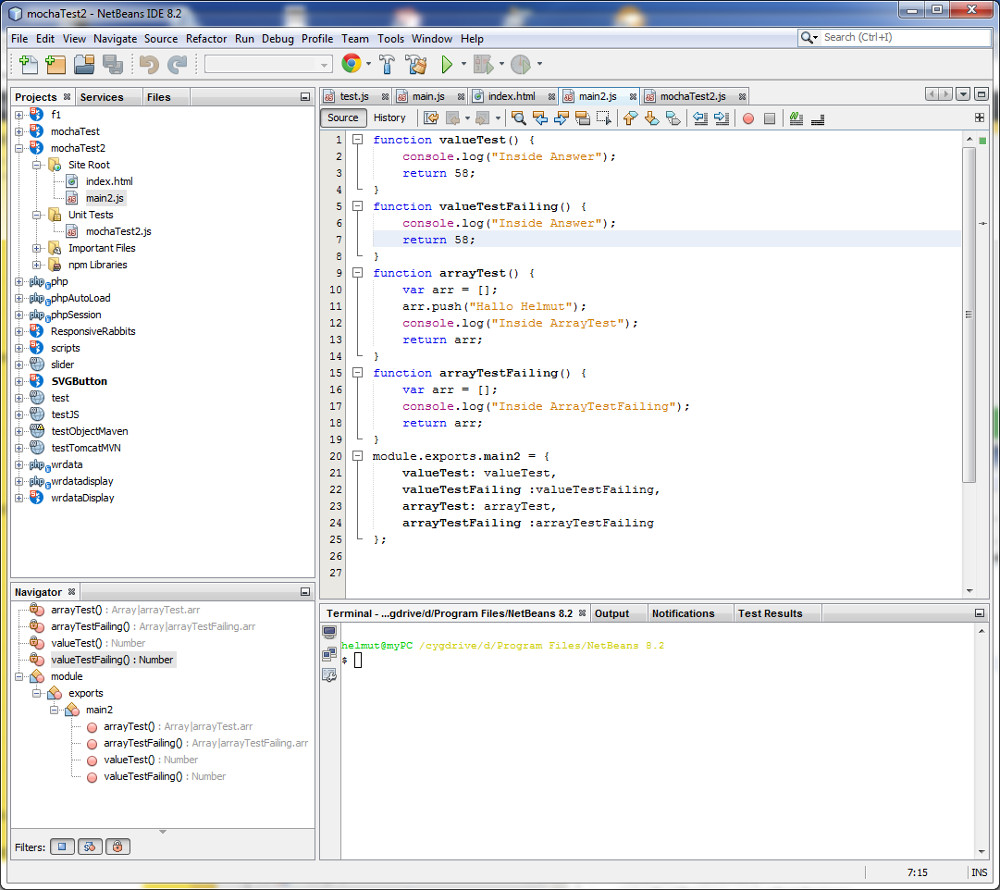
| Create a HTML5/Javascript Project and add Javascript File main2.js to the project |
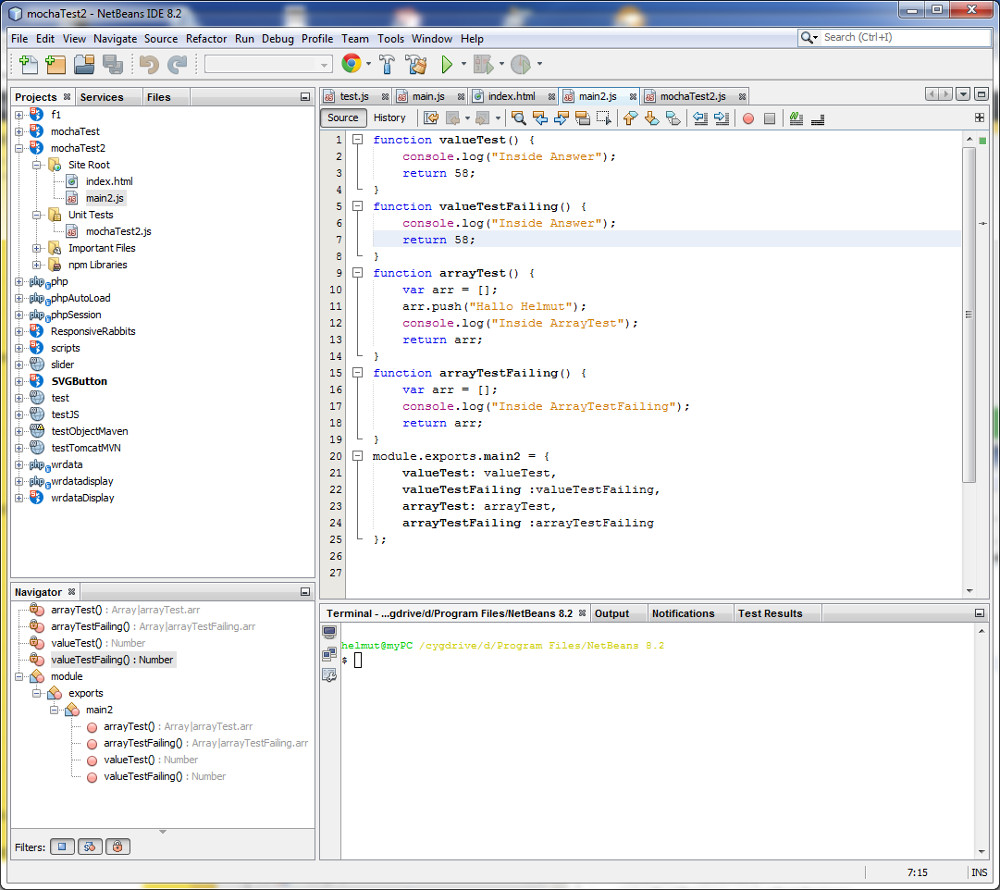 |
- Note: exports is a node.js concept that declares the functions that your module makes available to code outside itself
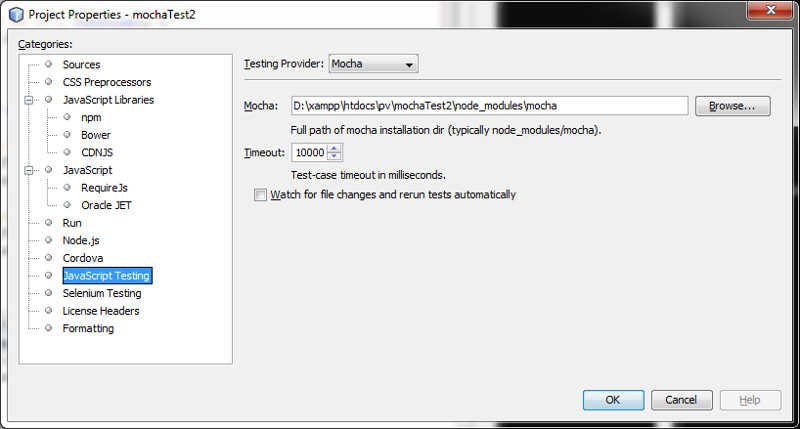
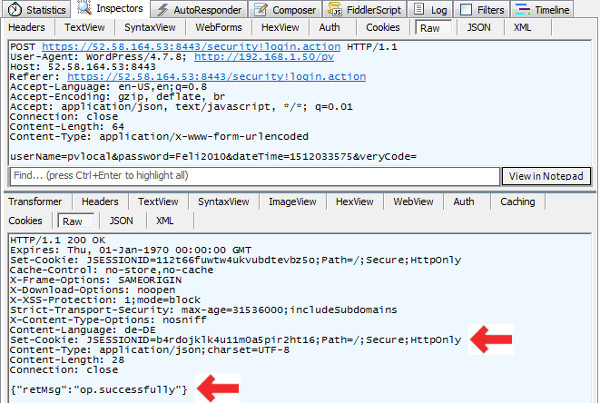
Setup Mocha as Testing Provider
| Change Project Properties for Javascript Testing |
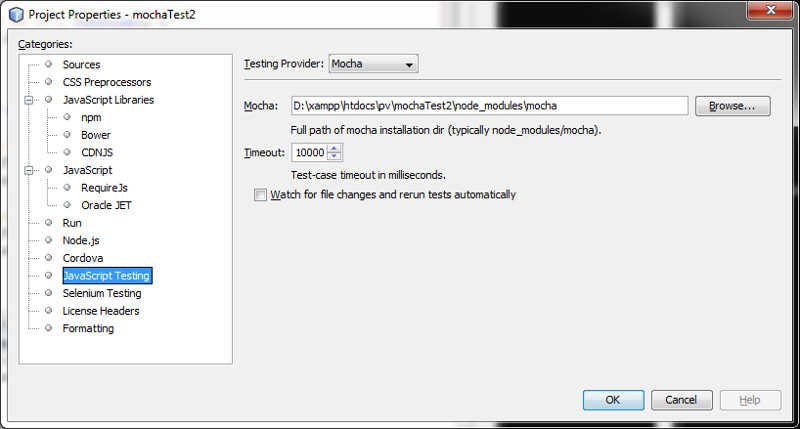 |
Setup Mocha/Chai [ Open a Netbeans Terminal Window]
Initialize new Node.js Project
$ cd D:\xampp\htdocs\pv\mochaTest2
$ npm init
This utility will walk you through creating a package.json file.
It only covers the most common items, and tries to guess sensible defaults.
See `npm help json` for definitive documentation on these fields
and exactly what they do.
Use `npm install ` afterwards to install a package and
save it as a dependency in the package.json file.
Press ^C at any time to quit.
package name: (mochatest2)
version: (1.0.0)
description: Mocha/Chai Testing
entry point: (index.js) main2.js
test command: mocha
git repository:
keywords:
author: Helmut
license: (ISC) MIT
About to write to D:\xampp\htdocs\pv\mochaTest2\package.json:
{
"name": "mochatest2",
"version": "1.0.0",
"description": "Mocha/Chai Testing",
"main": "main2.js",
"directories": {
"test": "test"
},
"scripts": {
"test": "mocha"
},
"author": "Helmut",
"license": "MIT"
}
Is this ok? (yes) yes
helmut@myPC /cygdrive/d/xampp/htdocs/pv/mochaTest2
Setup Mocha and Chai in our Netbeans Project Base Directory
helmut@myPC /cygdrive/d/xampp/htdocs/pv/mochaTest2
$ npm install mocha
npm WARN mochatest2@1.0.0 No repository field.
+ mocha@4.0.1
added 24 packages in 2.189s
helmut@myPC /cygdrive/d/xampp/htdocs/pv/mochaTest2
$ npm install chai
npm WARN mochatest2@1.0.0 No repository field.
+ chai@4.1.2
added 7 packages in 1.304s
Verify package.json – created by our previous setup steps
helmut@myPC /cygdrive/d/xampp/htdocs/pv/mochaTest2
$ cat package.json
{
"name": "mochatest2",
"version": "1.0.0",
"description": "Mocha/Chai Testing",
"main": "main2.js",
"directories": {
"test": "test"
},
"scripts": {
"test": "mocha"
},
"author": "Helmut",
"license": "MIT",
"dependencies": {
"chai": "^4.1.2",
"mocha": "^4.0.1"
}
}
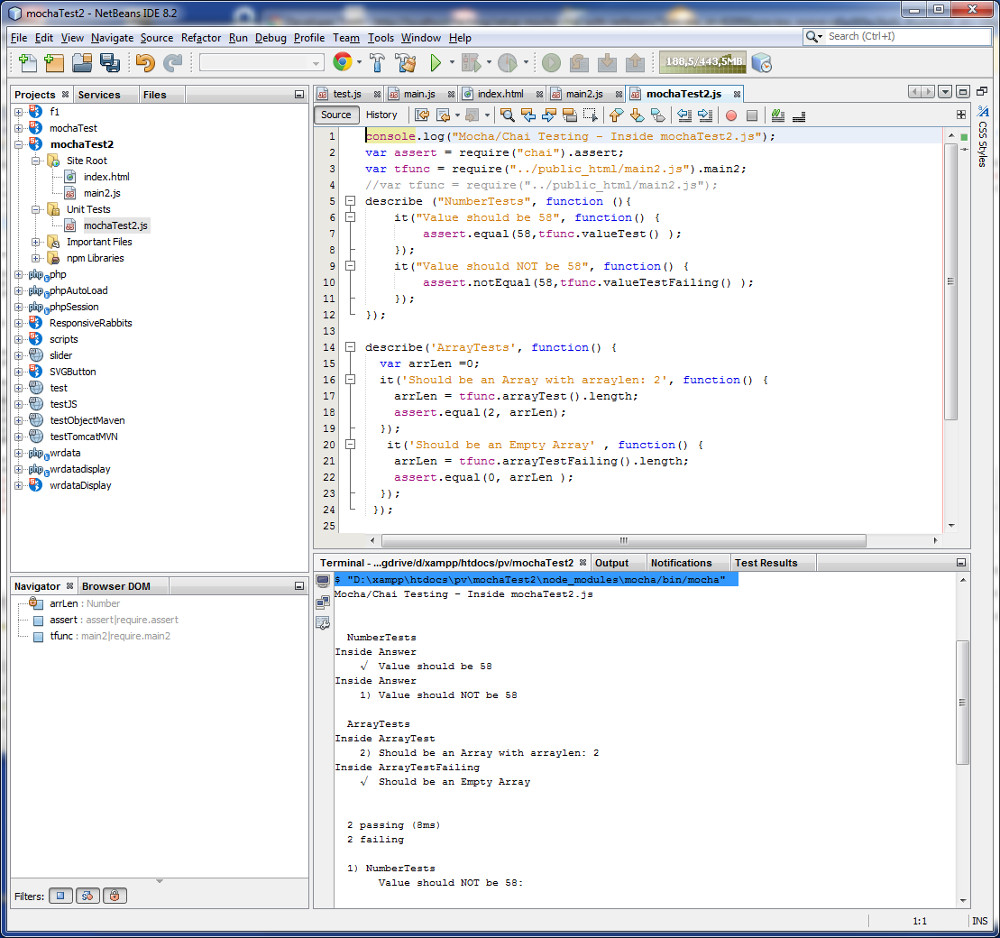
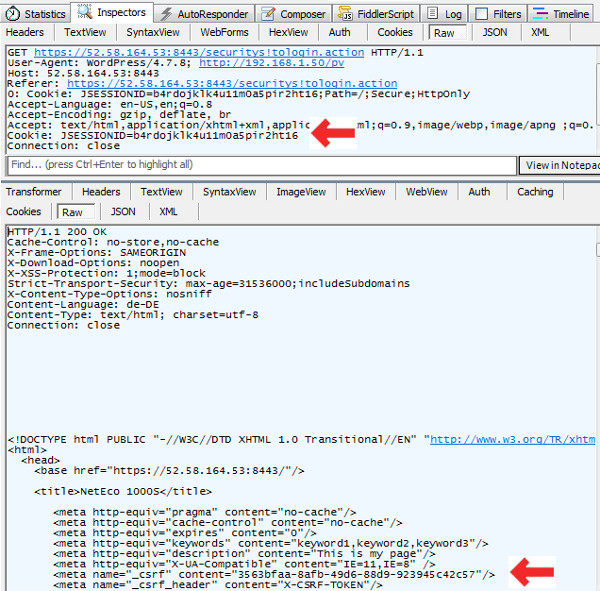
Create and Run Mocha testscript manually under Unit Test direcorty
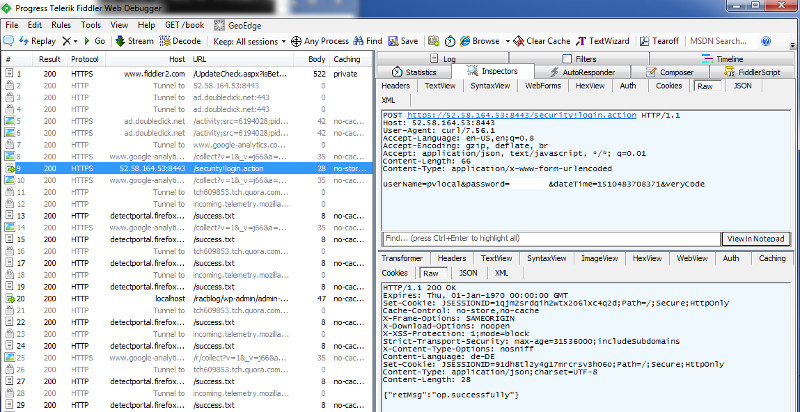
| Manually run Mocha Tests via Netbeans Terminal Window |
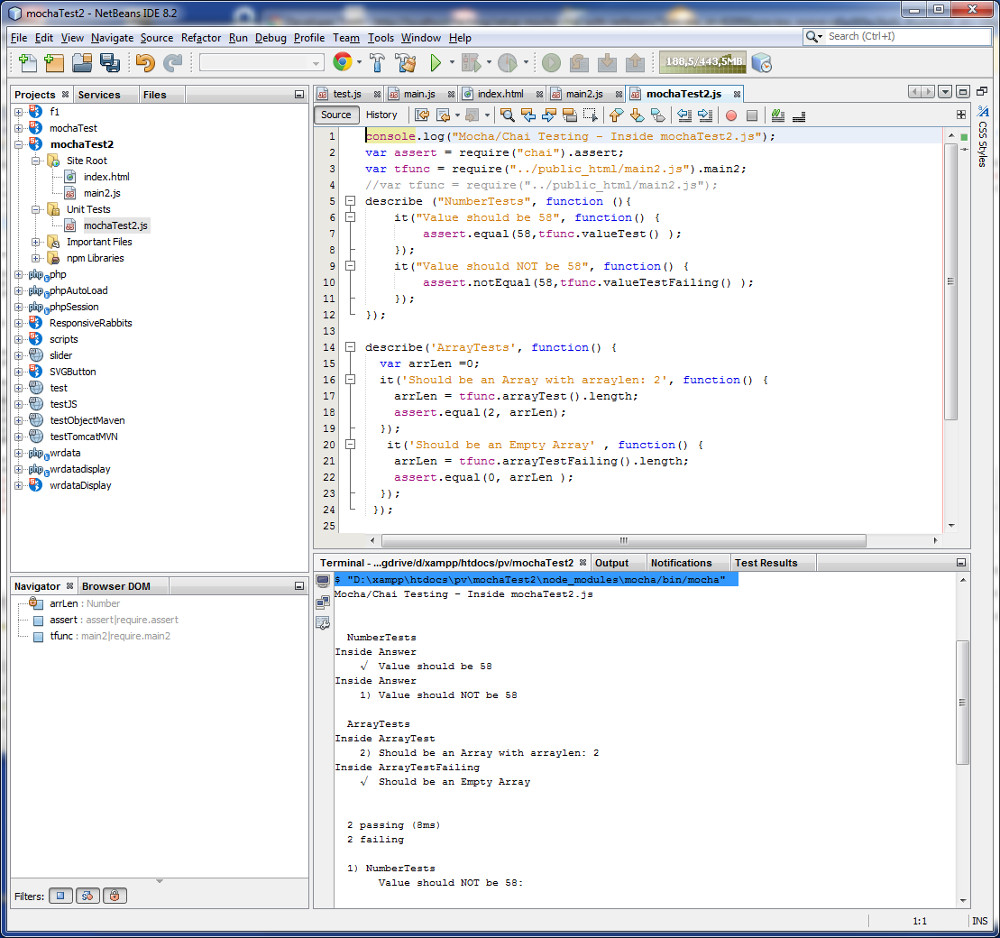 |
- Our test script mochaTest2.js imports the functions from Chai and main2.js via require()
- describe()` is merely used for grouping test Tests – can be nested if needed
- `it()` is a test case
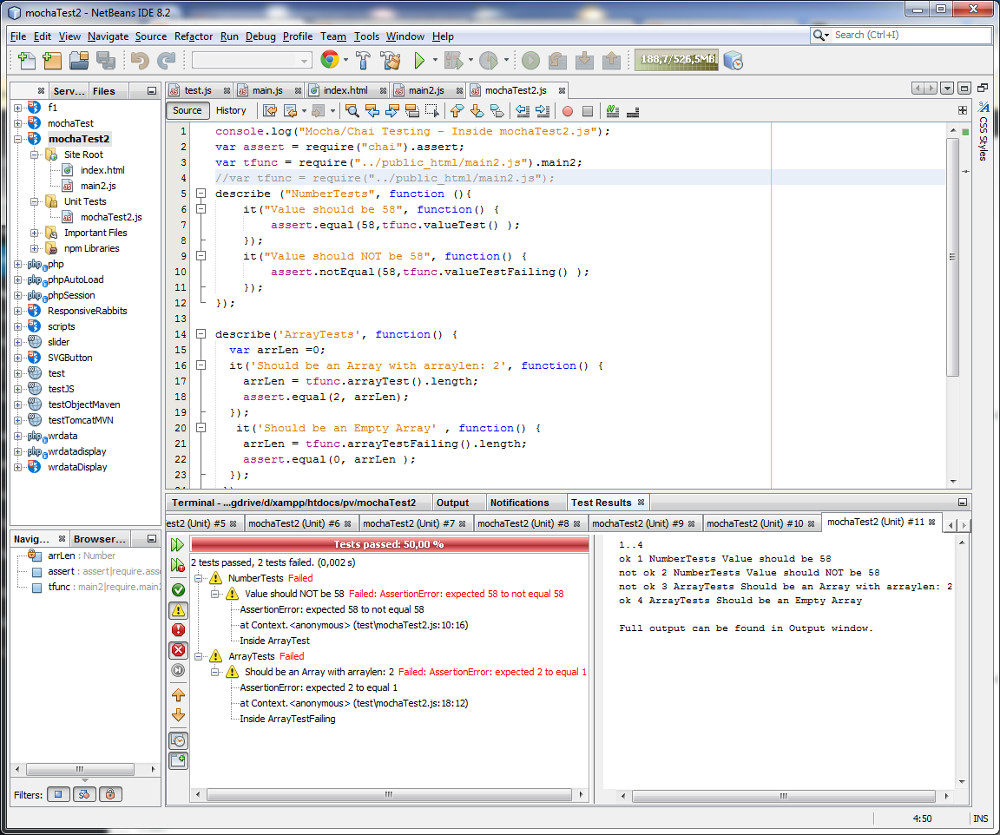
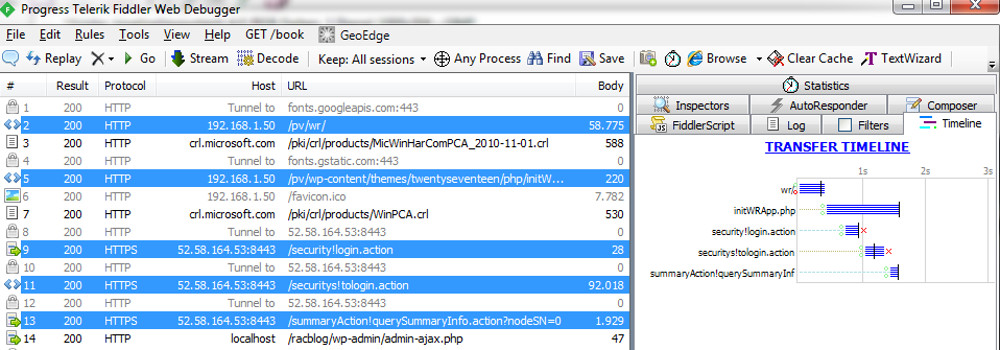
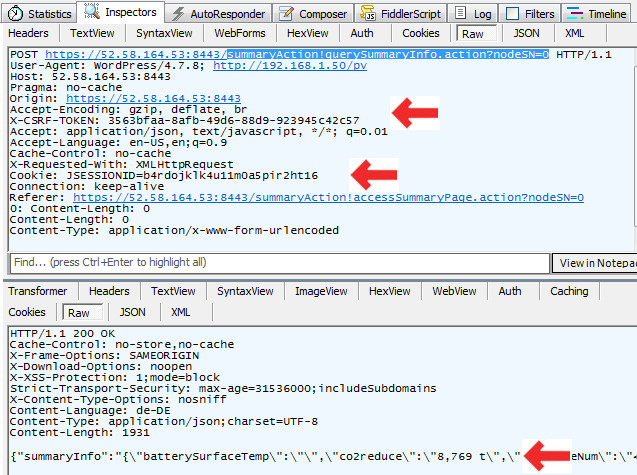
Finally run Neteans Unit Tests [ ALT F6]
| Open Netbeans Test Result Window to review Test Results |
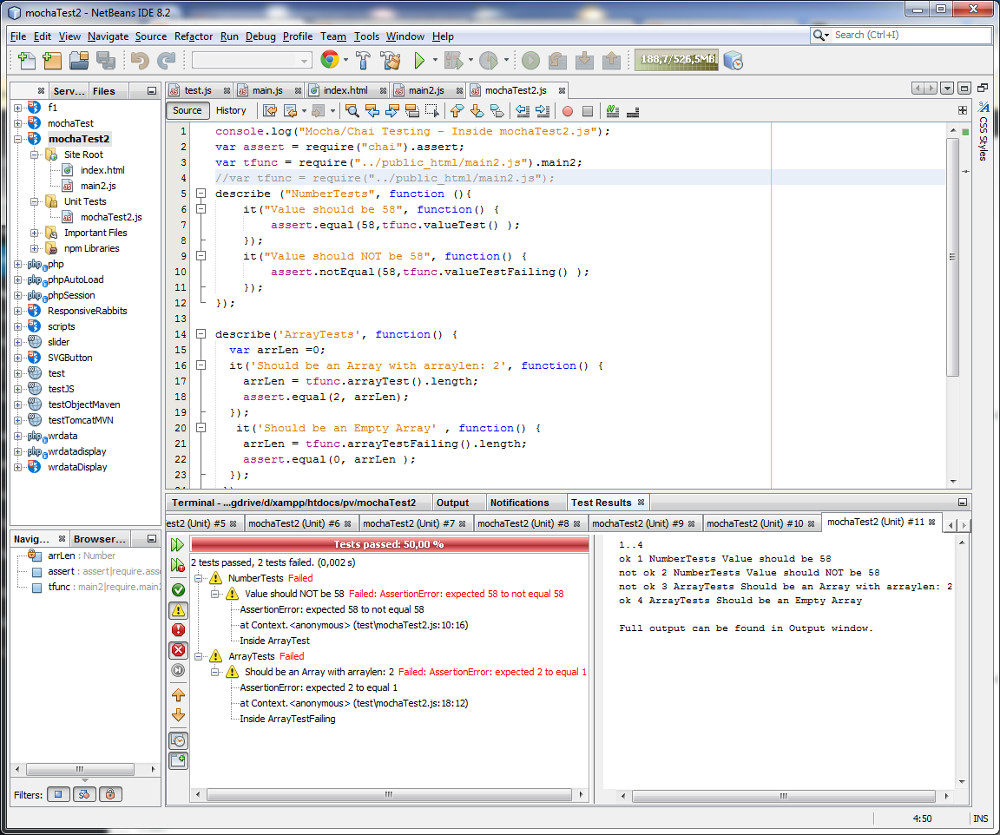 |
- Note: If Netbeans IDE hangs during Testing you may need to restart Netbeans to fix this !
Reference
How To Unit Testing JavaScript with Netbeans
Mocha Homepage
Working with package.json
An Absolute Beginner’s Guide to Using npm
Understanding module.exports and exports in Node.js